Keep Your Personal Information Safe with 2FA
Two-factor authentication (2FA) creates an extra layer of security that makes it harder for attackers to gain access to online information. If for some reason a hacker knows the password to your account as the result of a database breach or phishing campaign, the second factor of authentication will help to stop further access to your personal data.
What are authentication factors?
The ways in which someone can be authenticated usually fall into three categories known as the factors of authentication, which include:
1. Knowledge factors – something the user knows, such as a password, PIN or shared secret.
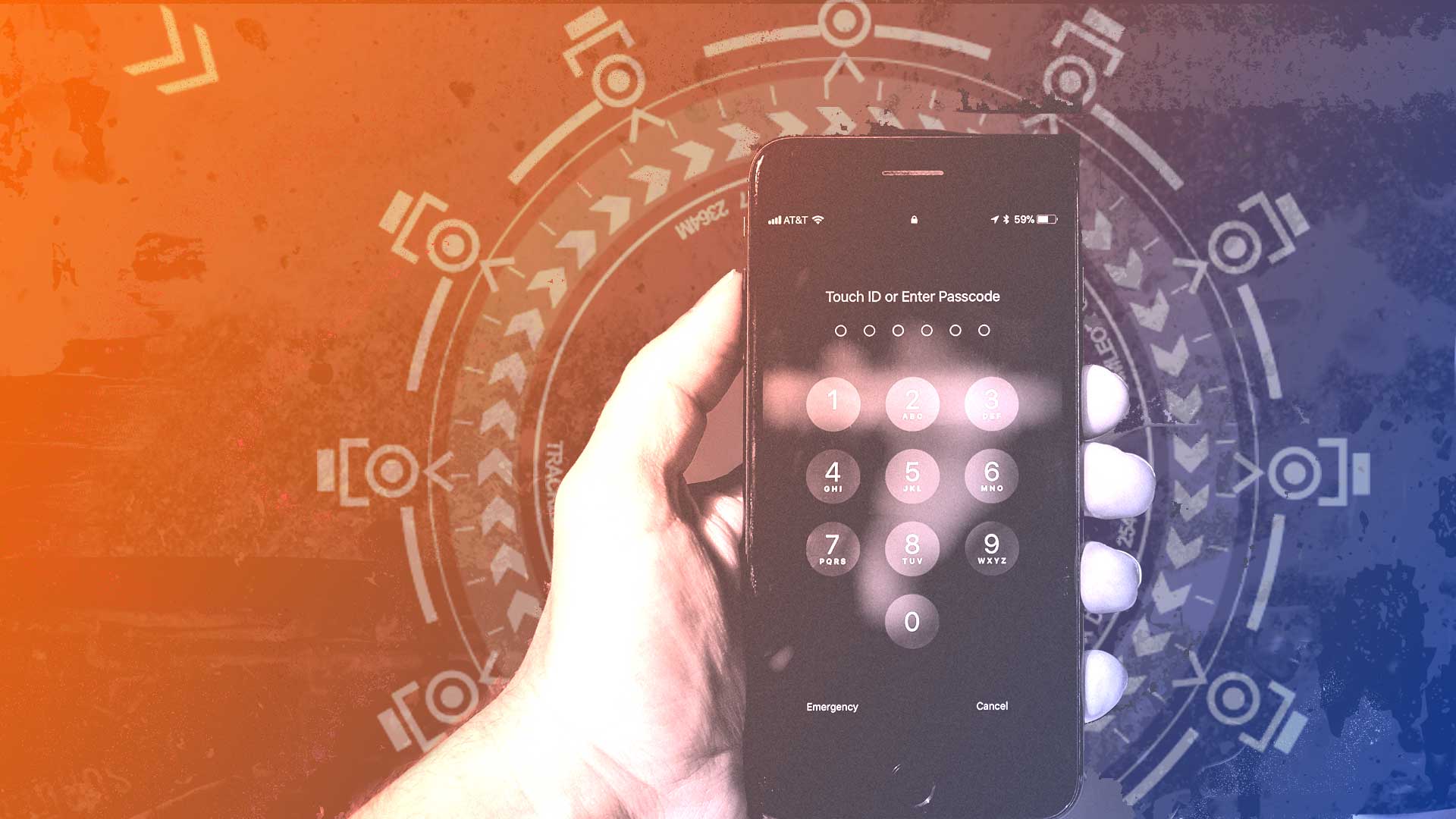
2. Possession factors – something the user has, such as an ID card, security token or a smartphone.
3. Inherence factors, more commonly called biometrics – something the user is. These may be personal attributes mapped from physical characteristics, such as fingerprints, face, and voice. It also includes behavioral biometrics, such as keystroke dynamics, gait or speech patterns.
Systems with more demanding requirements for security may use location and time as fourth and fifth factors. For example, users may be required to authenticate from specific locations, or during specific time windows.
A typical use of two-factor authentication is the combined use of a knowledge factor (Password or PIN) and a possession factor (verification code sent to your smartphone).
Although two-factor authentication may be viewed by some as a hassle due to the extra steps in the validation process, it is worth taking the extra measure to ensure the security of your personal information.
For additional information on two-factor authentication see the following link:
We can help make your info more secure.
For questions on protecting your online information, feel free to contact us at ZBx Technology.
